Backup and Recovery Policy Template
 Your disaster recovery plan needs to include policies and procedures for backup and restoration of individual computers and entire systems. Your goal is to have clear instructions for recovering your data.
Your disaster recovery plan needs to include policies and procedures for backup and restoration of individual computers and entire systems. Your goal is to have clear instructions for recovering your data.
2024 Edition now available
Special Offer Immediate Download Save 50% Limited time offer - Coupon Code Backup50off
Order Backup Policy Download Sample Backup Policy
Managing backup and recovery in today's environment is a multi-dimensional challenge with both near and long term business requirements. Recent technological developments in disk backup have had a positive impact on short term data retention requirements. But these improvements do not replace the need to execute and deliver on a long term data retention strategy which includes:- Business and Regulatory Requirements Demand a Long-term Plan
- Manage and Contain Your Total Cost of Ownership (TCO)
- Encrypt Your Data for Secure Long-term Retention
- Weigh the Environmental Impacts and Minimize Power and Cooling Costs
- Simplify Management of the Entire Solution
IT organizations of all sizes contend with a growing data footprint with more data to manage, protect, and preserve for longer periods of time. Online primary storage, has focus a on fast low latency, reliable access to data while near-line secondary storage has a focus on low cost and high capacity. Long-term data retention requires a combination of ultra-low cost, good performance during storage and retrieval, and reduced footprint in terms of power, cooling, floor-space and economics - also known as a small green footprint - for inactive data.
The Backup and Backup Retention Policy Template has been used to create customized policies for well over 2,000 enterprises world wide. This policy in concert with the Record Mangement Policy Template are must have Best Practices Tools for CIOs and IT professionals.
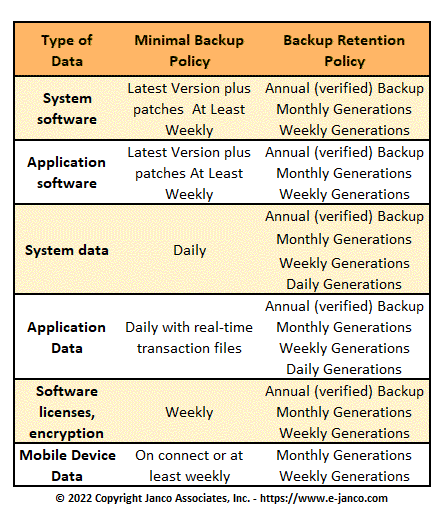
For example, factors that CIOs and IT professionals need to consider for backup retention include:
- Business and regulatory requirements – regulatory compliance and data preservation
- Economic and budgetary concerns – doing more with less
- Data loss prevention and information protection – protect, preserve and serve
- Environmental and business sustainment – green and economically efficient
- Maximize IT resource effectiveness and return on investment (ROI)
- Reduce total cost ownership (TCO) of IT resources and service delivery
Order Backup Policy Download Sample Backup Policy
Order Backup Policy Download Sample Backup Policy
CIO IT Infrastructure Policy Bundle
Janco has combine the policies that it has developed over time with some of the best IT organizations around the globe into a single package. With this bundle you get a PDF file that has all of the procedures in a single document that is over 300 pages long. It would take your staff months to develop these procedures from scratch. In addition you get a separate MS-Word document for each procedure which can easily be modified.
This bundle contains the following policies:
- Backup and Backup Retention Policy
- Blog and Personal Web Site Policy
- BYOD Policy Template
- Google Glass Policy Template
- Incident Communication Plan Policy
- Internet, e-Mail, Social Networking, Mobile Device, Electronic Communications, and Record Retention Policy
- Mobile Device Access and Use Policy
- Patch Management - Version Control Policy
- Outsourcing and Cloud Based File Sharing Policy
- Physical and Virtual Security Policy
- Record Management, Retention, and Destruction Policy
- Sensitive Information Policy
- Service Level Agreement (SLA) Policy Template with Metrics
- Social Networking Policy
- Telecommuting Policy
- Text Messaging Sensitive and Confidential Information
- Travel, Electronic Meeting, and Off-Site Meeting Policy
- Wearable Device Policy)
- IT Infrastructure Electronic Forms
Order IT Policy Bundle Download Sample Infrastructure Policies